User access and privilege users SUDO Implementation
In Operating System users has been categorized such that normal users ( all application , DB related user id’s , etc. would falls in this ) who is privilege to execute all commands under /usr/bin/ another one is administrative users or root users who has a privilege to execute the commands under /usr/bin/ and /usr/sbin.
Take an example bank locker access has been given to everyone (public) what would happen its un- imaginable. Such a way just imagine that root privilege has been grant to all the users who is part of that server what would happen simply even one would be playing with Operating System files etc …. Which would results unpredictable results even there is possibility for system crash.
Considering that is the system is part of test or used for some practices purpose we can tolerate , just imagine the system is part of production if someone missuses the privileged access would be landing in to serious issues and business impact as well.
But, sometime application/database users need root privilege to install or update or changing the configurations. Another scenario, in organization there would be multiple level of skill set people would be working it’s very difficult to grant root, database and application. That’s why access level categorization has been introduced whereas we able limit the access.
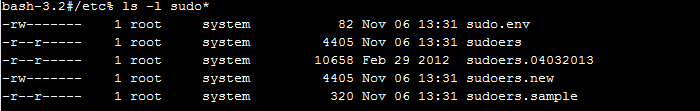
Here is an option to implement sudo in Operating System one is that open source rpm’s anther one is licensed. Once you install sudo package in Operating System under /etc/ sudo configuration files would be created over there i.e
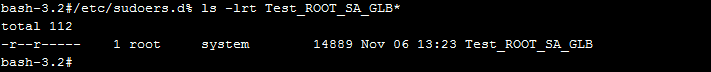
If you could see the below sudoers configuration file there would be a command alias row , whatever command you have add for the particular alias group add those commands and create an alias group. This is very much imparted and very careful while creating the alias group. Once alias group has been created along with commands create a group in /etc/sudoers file , in some cases depends upon the organization policy they would create a templates and which has been stored in to sudoers.d directory underneath all the templates has been stored. After that, in /etc/group have to create a group and add the users in to that group as per our definition in /etc/sudoers template the users would get the privileges.
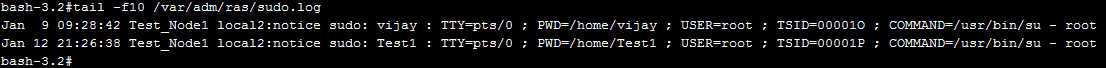
This method would avoid unnecessary access to the uses and make the users in to more accountable and secondary log control has been enabled via syslog which would keep the record of users who ever logged and which access group they have been switched.
In upcoming article we can see in detail about template creation and implementation as well. Hope this article help for an overview understanding about sudo privilege.
